Data breaches are an unfortunate norm in today's digital world, and traditional encryption techniques are no longer enough to prevent them. In addition, as businesses become more data-driven and regulations tighten, the pressure is on to rethink how we secure sensitive information, not just during storage but also throughout its entire life cycle.
How emerging tech is rewriting the rules of data security
5 Low-effort ways to make your office hardware last longer
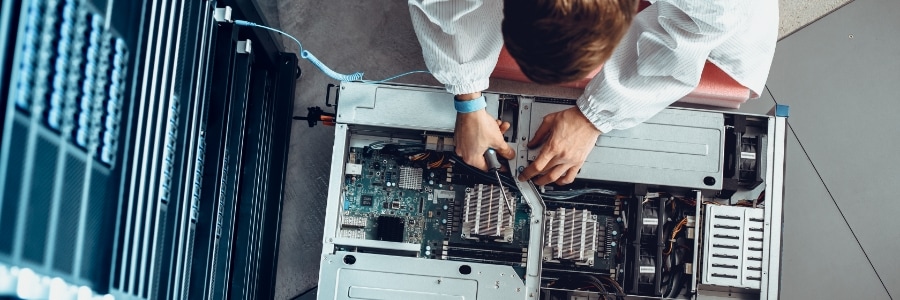
Keep your IT costs in check with smarter hardware habits. In this guide, we’ll walk you through simple, effective ways to maintain your business computers, printers, and workstations so they last longer and perform better.
Give your devices the treatment they deserve
Dust, fingerprints, and crumbs on your computers and monitors are unsightly and they can degrade hardware performance over time.
How Microsoft Copilot AI agents are changing the way we work

Artificial intelligence (AI) is fast becoming a key business tool, and Microsoft 365 Copilot is leading the way. The AI-powered tool now features new AI agents that help organizations boost productivity, simplify tasks, and expand its functionality. Here’s how these agents work and how to start using them to maximize your Microsoft 365 investment.
Private cloud pitfalls: Avoid these common setup mistakes

Setting up a private cloud often seems like the ideal solution for greater control, security, and scalability. However, there are common pitfalls that can disrupt the deployment process or hinder its long-term effectiveness. This article dives into the challenges organizations face when building and managing private cloud environments and how to tackle them effectively.
How AI is changing workplace surveillance
What everyday software teams can do to prevent the next big hack

Recent research shows many security checklists miss important safeguards, leaving systems open to cyberattacks. Fortunately, there are 10 actionable steps developers can implement immediately to build more secure applications. Dive in to discover these practical strategies and strengthen your software’s defenses.


